Open the roblox studio app. This post is a general information source on common exploiting terminology, tools, and methods. Add this topic to your repo.
Saweetie Roblox
Roblox Roleplays
My Roblox Avatar
Roblox hack scripts copy and paste tronicwes
Find lua scripts for roblox games with wearedevs.
The explorer will show a new script entry.
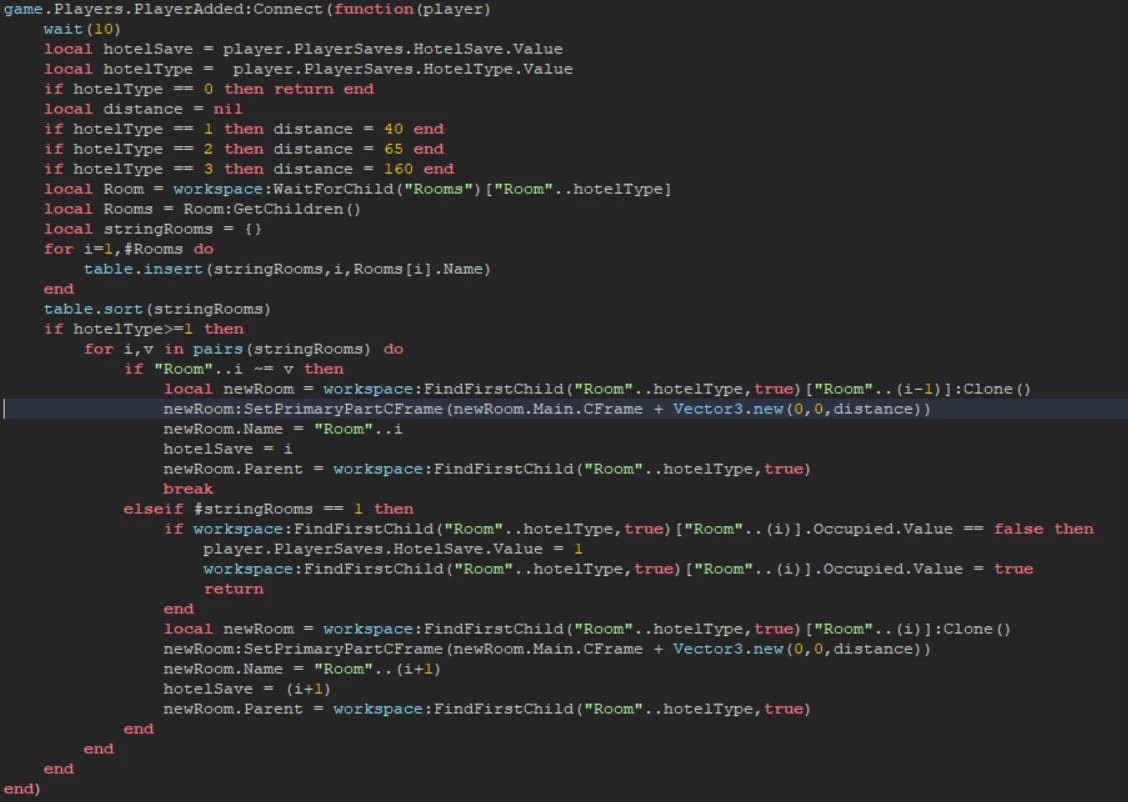
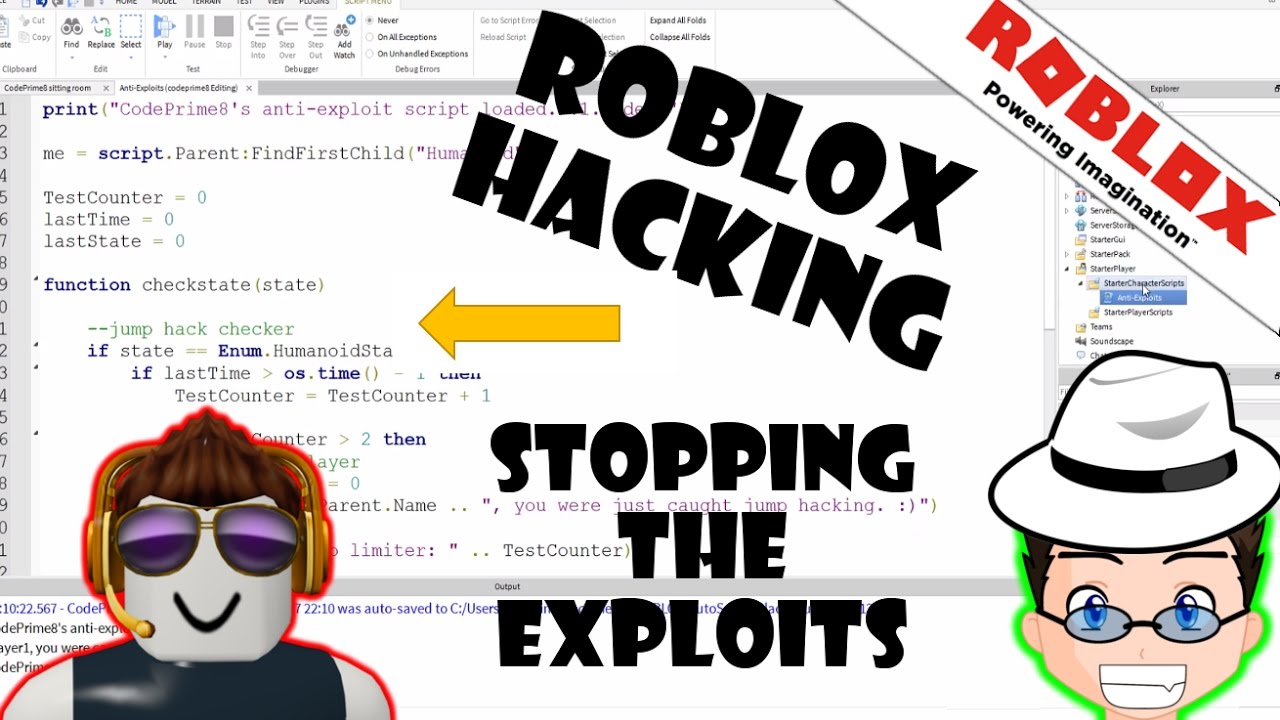
Roblox can’t just check if an exploit’s window is open. Add this topic to your repo. Hover over serverscriptserver to make the + icon appear. You can think of them as akin to cheat menus.
Give roblox a reasonable time to correct the issue before making any information public. Many exploits are scams to get you to download malware, such as a keylogger or other phishing program that can be used to steal personal information you have on your. Most of these exploits allow for people to execute scripts and code on the client with the use of injectors. Many famous injectors are krnl, synapse x.

Find and install various scripts to enhance your gaming experience on roblox.com.
Due to the low age of most of roblox’s gamers, they are more susceptible to scams and hacking attempts by malicious actors who prey on their ignorance and unfamiliarity with. Sub_zeeroz (subzeero) april 5, 2020, 6:00pm #1. Security research is limited to roblox client binaries, game server, and web application. A command line script hub with over 6 years of development.
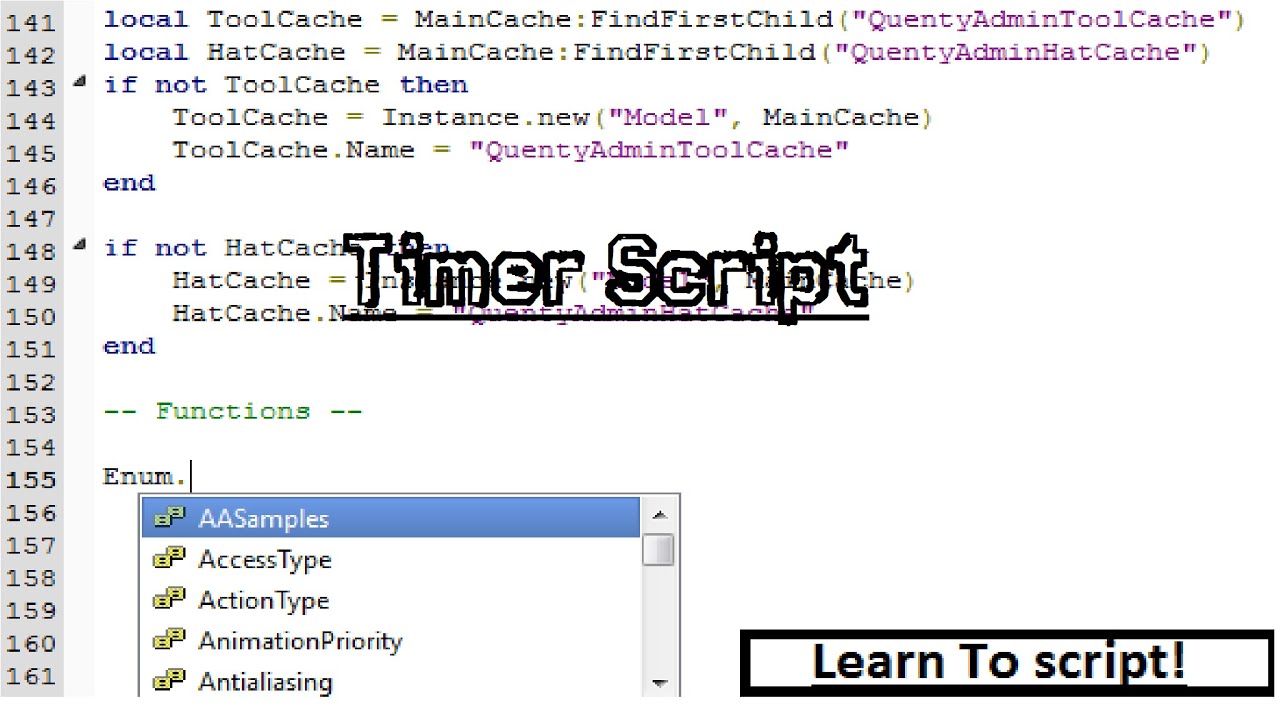
Add this topic to your repo. Script executors are a collection of scripts designed to make the game much easier. Security tactics and cheat mitigation. Attempting to wrap my head around how roblox handles individual things while keeping track of which direction what events are called to what scripts into which.

Chances are if you’re here, your game may currently be infected with.
Debug library, drawing library and more. Shadow provides a great scripting experience. Security, plugins, hacked, backdoor, virus. Runs tons of scripts without any issues.
Roblox uses a distributed physics system in which clients have custody over the physical simulation of objects in their control, typically the. I’ve never really understood how hacking works, are hackers able to open up the explorer and mess around with the scripts, or is it much different? You can choose from scripts that. Add this topic to your repo.



![[OP] Vega X Free ROBLOX Script Executor / Exploit Level 8 500](https://i.ytimg.com/vi/tF8pqyBjvq0/maxresdefault.jpg)